TL;DR:
With ransomware involved in roughly one-third of modern breaches and breach costs exceeding $4 million on average, enterprises must reinforce the 3-2-1 backup model. Separation, controlled access, monitoring, and tested recovery processes are now critical for reliable recovery.
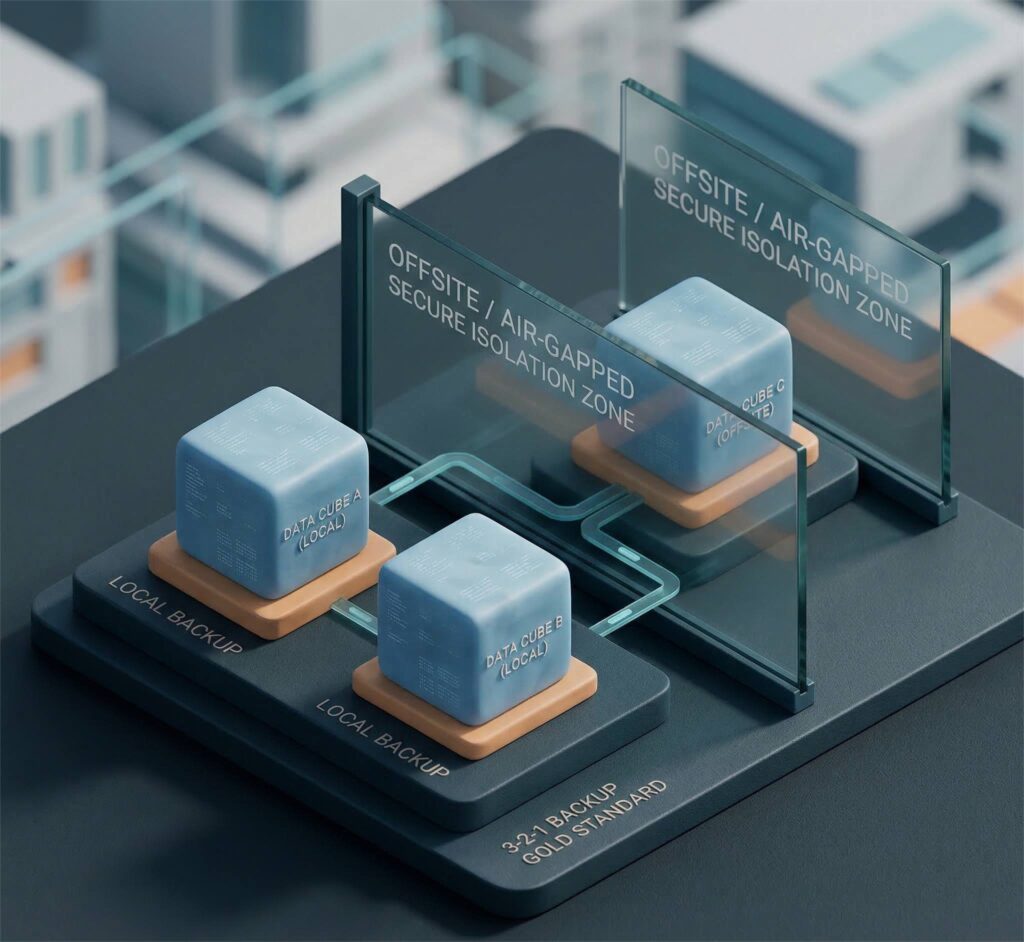
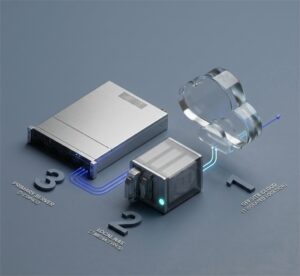
The 3-2-1 backup rule has long been the foundation of enterprise data protection: three copies of data, on two different media types, with one copy stored offsite. It remains a critical best practice.
But in 2026, resilience requires more than redundancy. According to IBM’s Cost of a Data Breach Report, the global average breach now costs organizations over $4 million, highlighting the financial impact of inadequate recovery strategies.
The 3-2-1 model is still essential, but it must be strengthened.
Strengthening the 3-2-1 Backup Rule for 2026
The 3-2-1 model still works. But it was designed for a different threat landscape, one that was dominated by hardware failures and natural disasters, not organized cybercrime.
These days, ransomware is systematic, deliberate, and often designed to undermine recovery itself.
According to the Verizon Data Breach Investigations Report (DBIR), roughly one-third of all breaches involved ransomware or other extortion techniques, with 23% involving ransomware and 9% involving pure extortion for a combined 32% of breaches.
Backup Systems Are Now Primary Targets
The Veeam Ransomware Trends Report found that in the majority of ransomware incidents studied, attackers specifically attempted to target backup repositories. In many cases, backup data was either encrypted or deleted before organizations could respond.
This changes the equation.
The original 3-2-1 rule assumes that multiple copies equal safety. But if those copies are accessible, modifiable, or deletable by compromised credentials, redundancy alone is insufficient.
True resilience requires ensuring that backup systems are properly isolated, access-controlled, and continuously monitored, so that recovery remains possible even during a coordinated attack.
What Enterprises Must Add in 2026
To withstand cyber threats, enterprises must go beyond maintaining multiple copies of data. They must add:
- Logical Separation
Backup environments should be isolated from production systems to limit lateral movement during an attack. - Strict Access Control
Administrative privileges should be limited, monitored, and protected with multi-factor authentication. - Continuous Monitoring
Backup activity must be tracked for unusual behavior, such as unexpected deletions or configuration changes. - Regular Recovery Testing
Backups should be restored periodically in controlled scenarios to verify that recovery works under realistic conditions.
These steps turn backup from a checklist item into a reliable recovery capability.
Strengthening a Proven Backup Foundation
These days, enterprises manage data across SaaS platforms, public clouds, hybrid infrastructure, and remote endpoints. A backup strategy must account not only for data duplication, but for how that data is accessed, segmented, and governed across environments.
As management thinker Peter Drucker famously said:
“The greatest danger in times of turbulence is not the turbulence, it is to act with yesterday’s logic.”
The 3-2-1 framework remains sound. What has changed is the threat behavior surrounding it.
Example: Consider a mid-sized enterprise operating across Microsoft 365, AWS infrastructure, and a SaaS project management platform.
They maintain:
- Production data
- A secondary backup copy
- An off-site cloud copy
On paper, the requirement is met. But if backup environments share the same privileged access controls as production systems, a compromised account could impact both. In that case, the vulnerability lies not in the number of copies, but in how they are protected.
Turning Backup into a Tested Recovery Strategy
Having backups is important. Knowing they will work when you need them is critical.
Many organizations run backups regularly but rarely test full recovery scenarios. During a real incident, however, systems may be unstable, credentials may be compromised, and teams may be under pressure. Recovery must work under those conditions.
A strong recovery strategy means:
- Clearly defining how quickly systems must be restored
- Knowing how much data loss is acceptable
- Testing restoration processes regularly
- Ensuring only authorized personnel can access backup systems
For example, backing up a collaboration platform every night is good practice. But can specific files, user accounts, or permissions be restored quickly? Can the business resume operations within the expected timeframe? These questions should be answered before an incident occurs.
As security expert Bruce Schneier has said:
“Security is a process, not a product.”
Backup resilience follows the same principle. It is not enough to configure backups once and assume protection. Recovery must be tested, validated, and treated as an ongoing operational discipline.
Summing Up
Cyber threats are more aggressive and more deliberate than ever. Ransomware is common, costly, and often targets recovery systems. Reliable recovery is about being able to restore operations quickly and confidently when something goes wrong.
In 2026, the organizations that recover fastest will be the ones that prepared deliberately.